You need to sign in to do that
Don't have an account?
Thawte SSL Certificate Problem
We have a client that is implementing a Mirth web service in their office and needs Salesforce data to be sent to it via SOAP web service.
We have the code working without the SSL certificate, but with the sertificate in place we are getting the following error when we call the web service method:
IO Exception: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
We have looked through the root certificates list provided by Salesforce:
https://developer.salesforce.com/page/Outbound_Messaging_SSL_CA_Certificates#thawteserverca (https://developer.salesforce.com/page/Outbound_Messaging_SSL_CA_Certificates#thawteserverca" target="_blank)
It appears our certificate is based on: thawteprimaryrootca (This is based on a comparison of the SHA1 fingerprint).
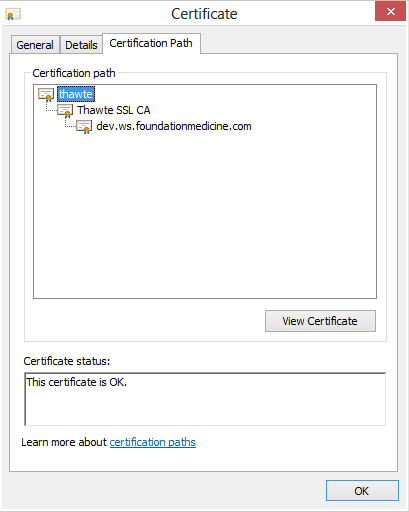
Our certificate chain looks like this:
The URL with the web service and the SSL certificate installed is at https://dev.ws.foundationmedicine.com/services/sfdc (https://dev.ws.foundationmedicine.com/services/sfdc" target="_blank)
We are concerned that there is a problem with the root certificate on the Salesforce server, and need to know how to proceed.
If anyone has encountered a similar problem, please reach out. Thanks in advance.
We have the code working without the SSL certificate, but with the sertificate in place we are getting the following error when we call the web service method:
IO Exception: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
We have looked through the root certificates list provided by Salesforce:
https://developer.salesforce.com/page/Outbound_Messaging_SSL_CA_Certificates#thawteserverca (https://developer.salesforce.com/page/Outbound_Messaging_SSL_CA_Certificates#thawteserverca" target="_blank)
It appears our certificate is based on: thawteprimaryrootca (This is based on a comparison of the SHA1 fingerprint).
Our certificate chain looks like this:
The URL with the web service and the SSL certificate installed is at https://dev.ws.foundationmedicine.com/services/sfdc (https://dev.ws.foundationmedicine.com/services/sfdc" target="_blank)
We are concerned that there is a problem with the root certificate on the Salesforce server, and need to know how to proceed.
If anyone has encountered a similar problem, please reach out. Thanks in advance.






 Apex Code Development
Apex Code Development
You will have to upload a full Certificate Chain
Digital certificates are verified using a chain of trust. The trust anchor for digital certificate is the root Certificate Authority (CA). Web browsers are preconfigured with a set of root CA certificates that the browser automatically trusts. Any certificate from elsewhere must come with a certificate chain to verify its validity.
A certificate chain is a sequence of certificates, where each certificate in the chain is signed by the subsequent certificate, eventually resulting in a tree structure. A certificate chain thus traces the path of a certificate from a branch to the root in the hierarchy. The root certificate is a self-signed, topmost certificate of the tree and is generated first. A self-signed certificate is one for which the issuer (signer) is the same as the subject (the entity whose public key is being authenticated by the certificate). The certificates that are directly subordinate to the root certificate have CA certificates that are signed by the root certificate. All certificates below the root certificate thus inherit the trustworthiness of the root certificate.
A certificate chain has the following components:
A root CA certificate
One or more intermediate certificates
Client/server certificate signed by the intermediate CA certificate
In a certificate chain:
Each certificate is followed by the certificate of its issuer. The certificate contains the distinguished name of the certificate's issuer and is same as the subject name of the next certificate in the certificate chain.
Each certificate is signed with a private key of its issuer. The signature can be verified with the public key in the issuer's certificate, which is the next certificate in the certificate chain.
Verifying a certificate chain is a process of ensuring that a specific chain is valid, correctly signed, and trustworthy. The purpose of certificate chain is to establish a chain of trust from a subordinate certificate to a trusted root CA certificate. The root CA certificate vouches for the identity in the branch certificate by signing it. If the root CA is the one you trust, it implies that you can trust the certificate of its branches.
During a certificate chain verification, the authentication will fail when:
The root CA is not trusted
An invalid signature is found
The certificate validity dates are expired
Installing a Certificate Chain
Login to the Admin Console.
Click Edit Configuration from Common Tasks > Configuration Tasks.
Click the Certificates > Certificate Authorities tab from the Configurations page.
Click the Install... tab from the Certificate Authorities (CAs) page.
An Install CA Certificate Wizard opens. The wizard guides you through the settings available for installing a Certificate Chain. The following sections provide a description of the fields available in the wizard pages:
Step1:Select Tokens and Passwords
This wizard page enables you to set a token from a list of available tokens for the configuration and to enter the
password for the same.
Select the Token (CryptographicDevice) which contains the keys. If your key is stored in the local key database
maintained by the server, choose Internal. If your key is stored in a Smart Card or other external device or engine,
choose the name of the external token from the drop-down list box. Enter the Password for the selected token.
Step2:Enter Certificate Data
This wizard page enables you to enter certificate data along with the headers in the text area or provide the path to
a file containing the certificate data.
Paste the certificate text in the text area provided. When you copy and paste the text, be sure to include the headers
"Begin Certificate" and "End Certificate" — including the beginning and ending hyphens.
Step3:Certificate Type
This wizard page enables you to choose the type of certificate to be installed.
Select Certificate Chain as Certificate Type.
Step4:Review
This page provides you with a summary of selected options. Click Finish to complete the installation process.
Step5:Results
This wizard page displays the results of Install CA certificate action.
The CA Certificate is installed successfully.
Yhanks,
Amit Bhardwaj